Black Hat Go. Programming for Hackers and Pentesters
Black Hat Go explores the dark sides of Go — a popular programming language that is highly valued by hackers for its simplicity, efficiency, and reliability. This book — an arsenal of practical techniques for security professionals and hackers —...
will assist you in testing systems, creating and automating tools, as well as improving your threat countermeasure skills. All of this is achieved through the extensive capabilities of Go.
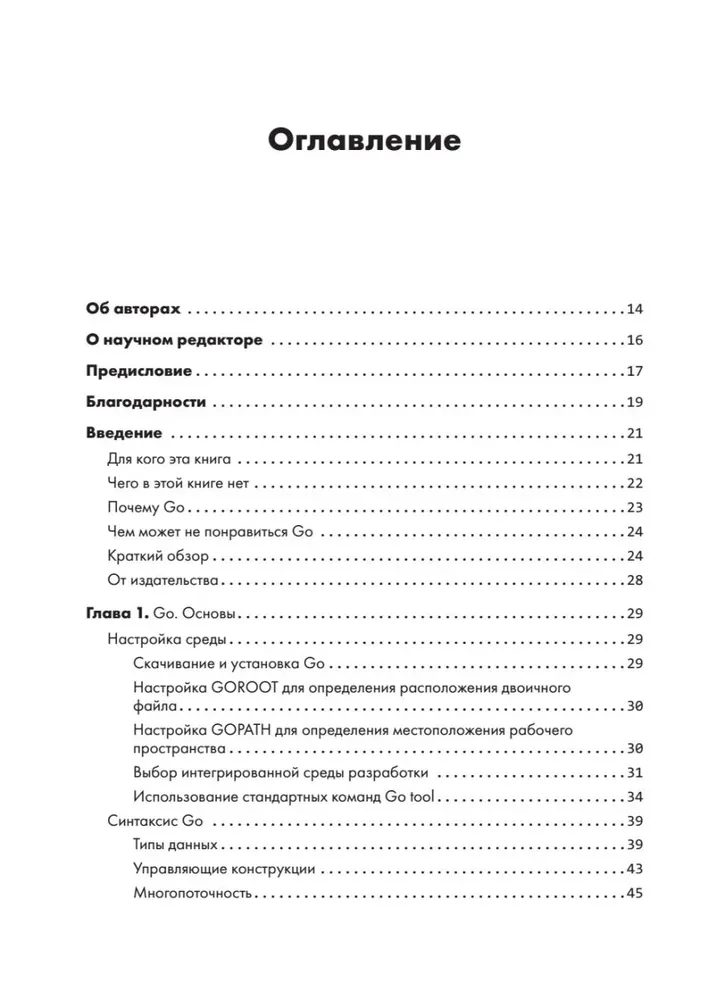
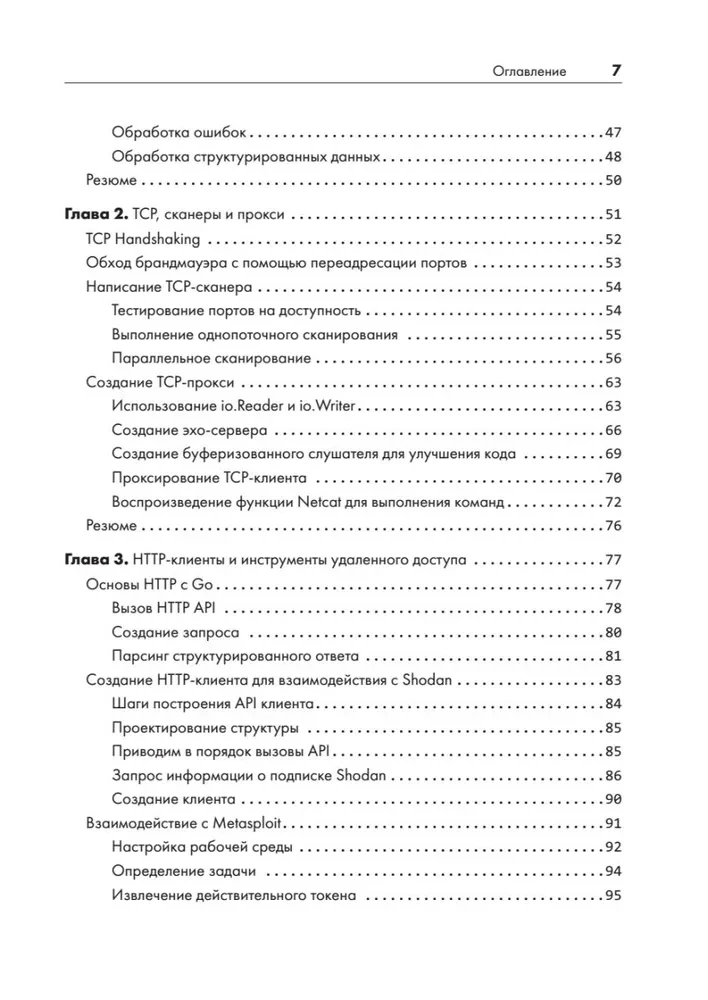
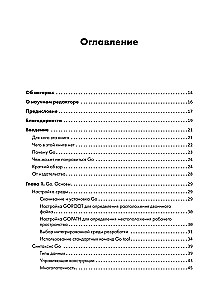
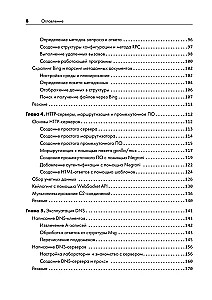
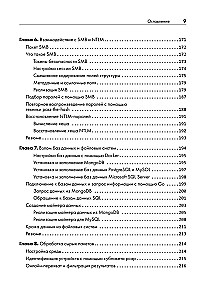
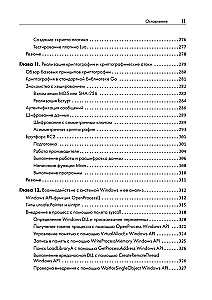
You will start with a basic overview of the language's syntax and the philosophy behind it, after which you will move on to studying examples useful for tool development. You will familiarize yourself with the HTTP, DNS, and SMB protocols. Next, you will delve into various tactics and tasks that pentesters encounter, covering topics such as data theft, network packet sniffing, and exploit development. You will learn to create dynamic embedded tools before moving on to the study of cryptography, attacks on Windows, and steganography.
Ready to expand your security tool arsenal? Then let's go!
You will start with a basic overview of the language's syntax and the philosophy behind it, after which you will move on to studying examples useful for tool development. You will familiarize yourself with the HTTP, DNS, and SMB protocols. Next, you will delve into various tactics and tasks that pentesters encounter, covering topics such as data theft, network packet sniffing, and exploit development. You will learn to create dynamic embedded tools before moving on to the study of cryptography, attacks on Windows, and steganography.
Ready to expand your security tool arsenal? Then let's go!
Author: Том Стил, Крис Паттен, Дэн Коттманн
Printhouse: piter
Series: Programmer's Library
Age restrictions: 16+
Year of publication: 2025
ISBN: 9785446117956
Number of pages: 384
Size: 233x165x20 mm
Cover type: soft
Weight: 600 g
ID: 1508970
Available from suppliers
Estimated delivery time – up to 3 weeks
€ 27.09
Available from suppliers
Estimated delivery time – up to 3 weeks
€ 27.09