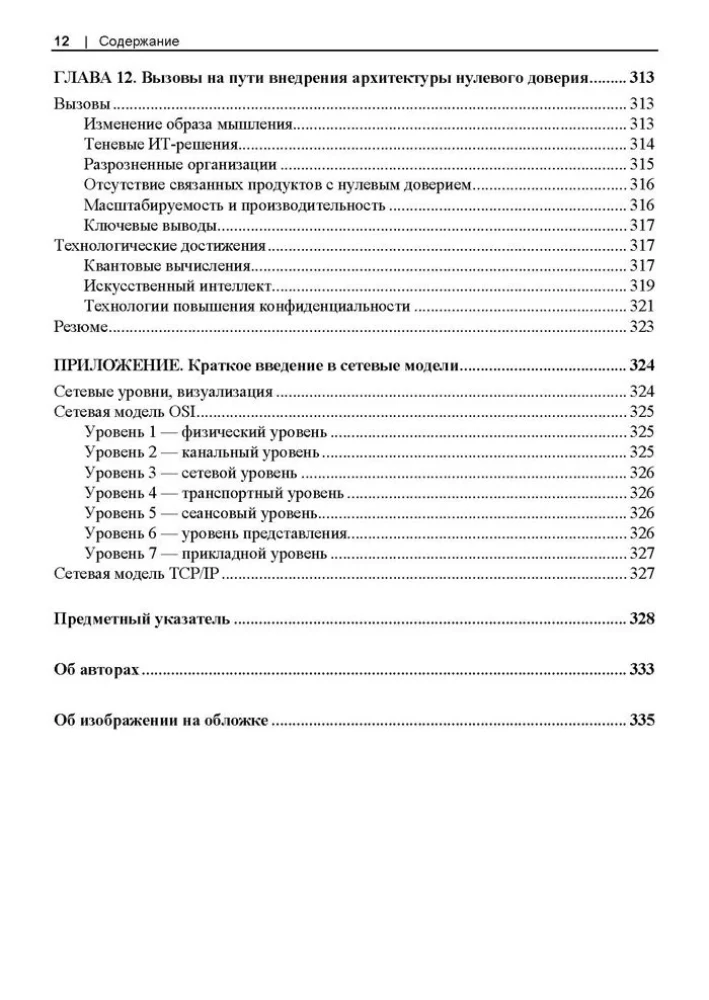
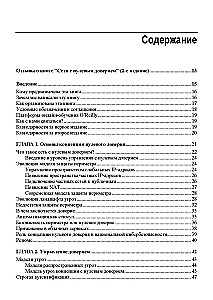
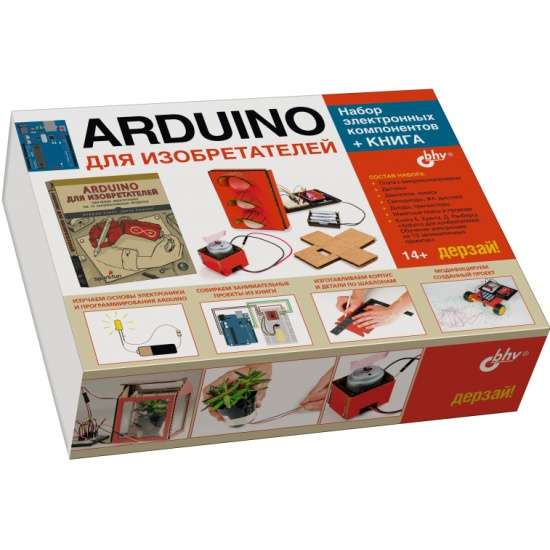
Zero Trust Networks
Author: Рази Райс, Кристина Морильо, Эван Гилман, Дуг Барт
Printhouse: BHV
Age restrictions: 16+
Year of publication: 2025
ISBN: 9786011234672
Number of pages: 336
Size: 250х170х15 mm
Cover type: soft
Weight: 432 g
ID: 1738642
from € 38.94