Transparent Software. Software Supply Chain Security
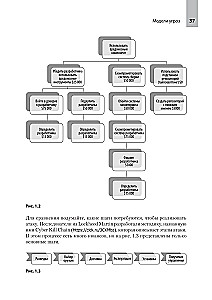
Can software supply chains be secure? A team of dedicated professionals offers a fresh perspective on your organization's security. You'll get acquainted with a variety of topics: from the history of... the transparency movement in software to approaches for specification and validation in the rapidly evolving software landscape.
The authors introduce us to the main attack vectors, such as mobile and social networks, banking systems, retail systems, and even critical infrastructures, as well as the protective systems we all rely on. You will learn how to defend against threats and gain practical recommendations for both software consumers and providers.
"Transparent Software" is a valuable source of knowledge for cybersecurity and application security professionals, as well as for those working in the field of industrial control system security, cloud security, mobile security, DevOps, and DevSecOps. 5 reasons to read: Embedded software. Cloud and other external APIs. Industrial control systems. Internet of Things connected devices. Mobile device software.
Author: Крис Хьюз, Тони Тернер
Printhouse: piter
Series: For Professionals
Age restrictions: 16+
Year of publication: 2025
ISBN: 9785446121823
Number of pages: 352
Size: 233х165х18 mm
Cover type: soft
Weight: 556 g
ID: 1688304
from € 38.94


-medium.webp)